
Resolution of ISAKMP/Oakley key-agreement protocol resistant against denial-of-service attack | Semantic Scholar

Resolution of ISAKMP/Oakley key-agreement protocol resistant against denial-of-service attack | Semantic Scholar

Resolution of ISAKMP/Oakley key-agreement protocol resistant against denial-of-service attack | Semantic Scholar
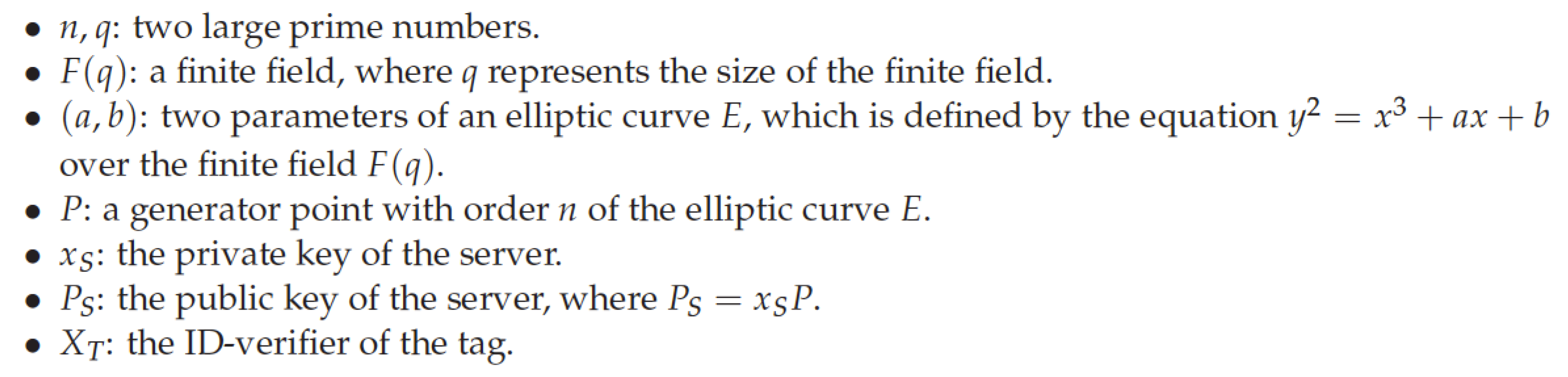


![Operation of SA other protocols: OAKLEY, SKEME and ISAKMP [8] [5].... | Download Scientific Diagram Operation of SA other protocols: OAKLEY, SKEME and ISAKMP [8] [5].... | Download Scientific Diagram](https://www.researchgate.net/profile/Riaz_Khan10/publication/297336095/figure/fig4/AS:558684922224640@1510212273285/Operation-of-SA-other-protocols-OAKLEY-SKEME-and-ISAKMP-8-5-OAKLEY-it-is-a-key_Q320.jpg)
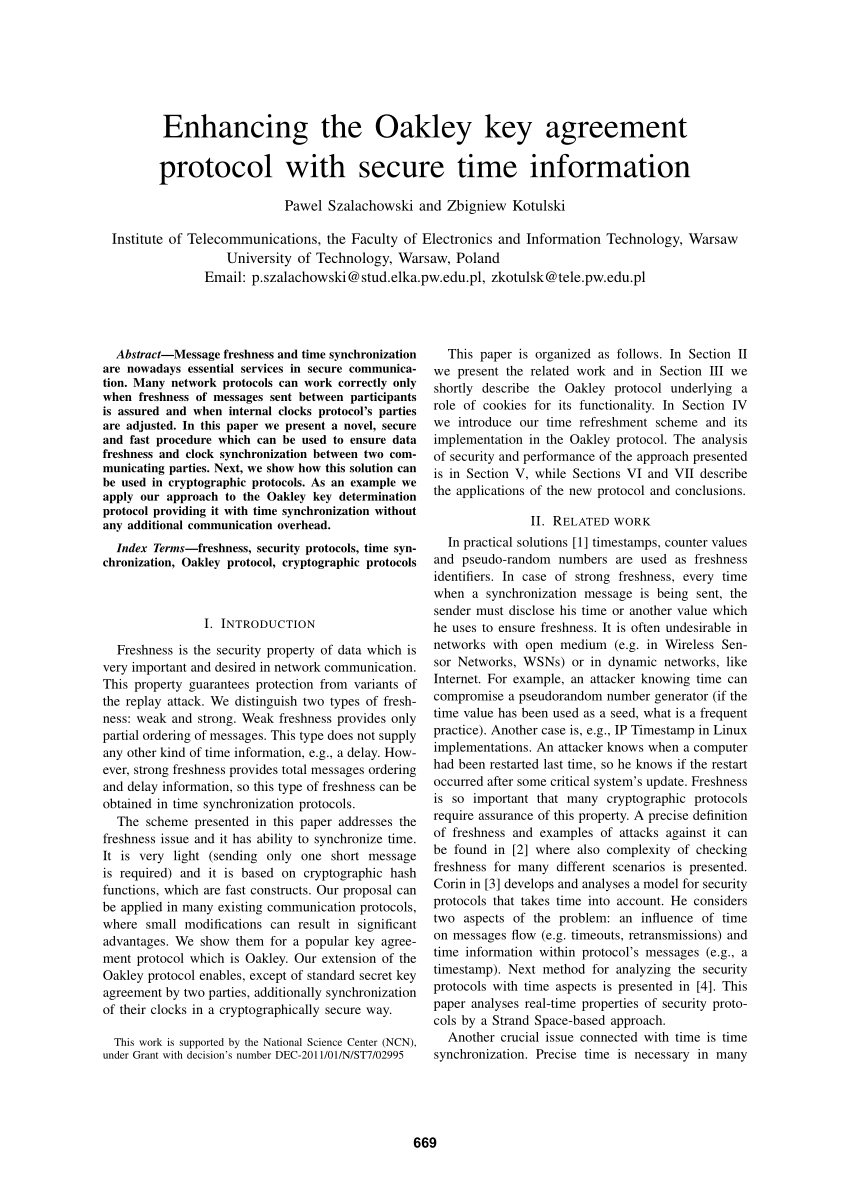
![PDF] Enhancing the Oakley key agreement protocol with secure time information | Semantic Scholar PDF] Enhancing the Oakley key agreement protocol with secure time information | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/abf5a6368d10fcb9adbdffc11d44a0228ba70b4b/4-Figure1-1.png)
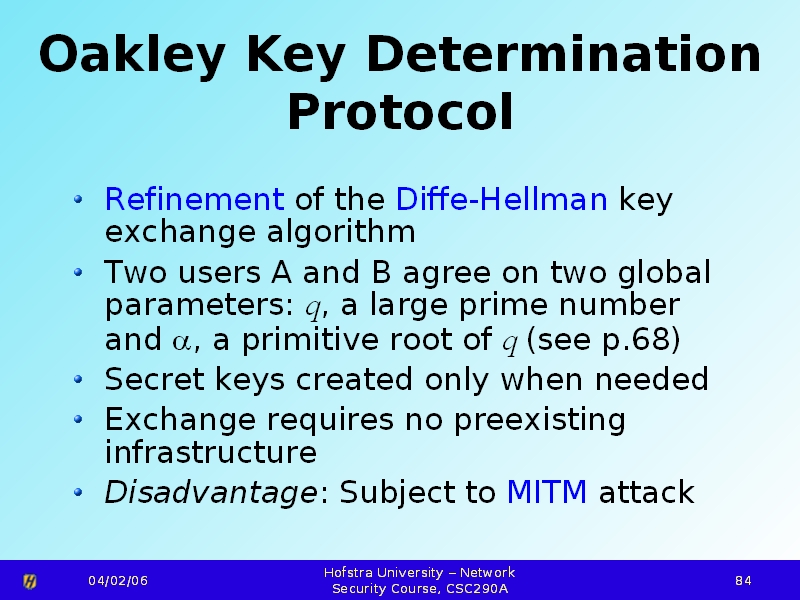
![Operation of SA other protocols: OAKLEY, SKEME and ISAKMP [8] [5].... | Download Scientific Diagram Operation of SA other protocols: OAKLEY, SKEME and ISAKMP [8] [5].... | Download Scientific Diagram](https://www.researchgate.net/profile/Riaz_Khan10/publication/297336095/figure/fig2/AS:558684922814464@1510212273166/ESP-Header-Format_Q320.jpg)





![Operation of SA other protocols: OAKLEY, SKEME and ISAKMP [8] [5].... | Download Scientific Diagram Operation of SA other protocols: OAKLEY, SKEME and ISAKMP [8] [5].... | Download Scientific Diagram](https://www.researchgate.net/profile/Riaz_Khan10/publication/297336095/figure/fig4/AS:558684922224640@1510212273285/Operation-of-SA-other-protocols-OAKLEY-SKEME-and-ISAKMP-8-5-OAKLEY-it-is-a-key.png)
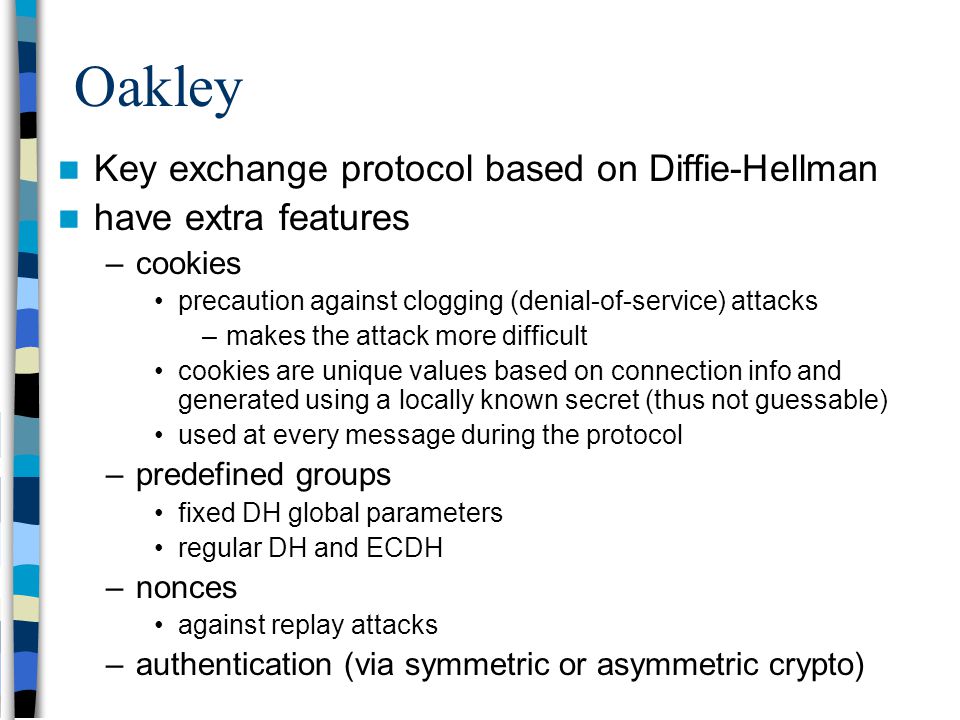


![PDF] Enhancing the Oakley key agreement protocol with secure time information | Semantic Scholar PDF] Enhancing the Oakley key agreement protocol with secure time information | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/abf5a6368d10fcb9adbdffc11d44a0228ba70b4b/6-Figure5-1.png)